NSA gets data from Germany’s domestic security agency
Posted By kurtnimmoadmin On September 14, 2013 @ 8:47 am In Big Brother,Tile
rt.com
September 14, 2013

Demonstrators hold up a placard featuring German Chancellor Angela Merkel in front of Berlin’s landmark Brandenburg Gate as they take part in a protest against the US National Security Agency (NSA) collecting German emails, online chats and phone calls and sharing some of it with the country’s intelligence services in Berlin on July 27, 2013. (AFP Photo)
Germany’ Federal Office for the Protection of the Constitution regularly hands over classified data to the NSA, media report. The revelation comes as Edward Snowden’s leaks show that Germany’s foreign spy agencies share troves of data with the US and UK.
Citing secret government documents, Suddeutsche Zeitung reported that Germany’s Federal Office for the Protection of the Constitution, charged with domestic security, works closely with the US and regularly sends them information.
The security service gathers intelligence on internal security threats. The documents obtained by Sueddeutsche Zeitung recorded 864 data packages sent to the NSA, as well as regular meetings between officers of the German Federal Office and the NSA.
URL to article: http://rt.com/news/germany-shares-data-nsa-spying-858/
NSA disguised itself as Google to spy on you
Posted By kit On September 13, 2013 @ 2:04 pm In Big Brother,Tile
Edward Moyer
Cnet
September 13, 2013
Here’s one of the latest tidbits on the NSA surveillance scandal (which seems to be generating nearly as many blog items as there are phone numbers in the spy agency’s data banks).
Earlier this week, Techdirt picked up on a passing mention in a Brazilian news story and a Slate article to point out that the US National Security Agency had apparently impersonated Google on at least one occasion to gather data on people. (Mother Jones subsequently pointed outTechdirt’s point-out.)
Brazilian site Fantastico obtained and published a document leaked by Edward Snowden, which diagrams how a “man in the middle attack” involving Google was apparently carried out.
A technique commonly used by hackers, a MITM attack involves using a fake security certificate to pose as a legitimate Web service, bypass browser security settings, and then intercept data that an unsuspecting person is sending to that service. Hackers could, for example, pose as a banking Web site and steal passwords.

The article by Brazil’s Fantastico mentions a hitherto unknown GCHQ spy program called “Flying Pig.” This prompted a Twitter quip from Electronic Frontier Foundation attorney Kurt Opsahl: “PRISM, Flying Pig. Someone in the surveillance state has a thing for Pink Floyd album covers.”(Credit: Pig: Musiclipse.com; prism: Harvest, Capitol.)
The technique is particularly sly because the hackers then use the password to log in to the real banking site and then serve as a “man in the middle,” receiving requests from the banking customer, passing them on to the bank site, and then returning requested info to the customer — all the while collecting data for themselves, with neither the customer nor the bank realizing what’s happening. Such attacks can be used against e-mail providers too.
It’s not clear if the supposed attack in the Fantastico document was handled by the NSA or by its UK counterpart, the Government Communications Headquarters (GCHQ). The article by the Brazilian news agency says, “In this case, data is rerouted to the NSA central, and then relayed to its destination, without either end noticing.”
“There have been rumors of the NSA and others using those kinds of MITM attacks,” Mike Masnick writes on Techdirt, “but to have it confirmed that they’re doing them against the likes of Google… is a big deal — and something I would imagine does not make [Google] particularly happy.”
Google provided a short statement to Mother Jones reporter Josh Harkinson in response to his questions on the matter: “As for recent reports that the US government has found ways to circumvent our security systems, we have no evidence of any such thing ever occurring. We provide our user data to governments only in accordance with the law.” (The company is also trying to win the right toprovide more transparency regarding government requests for data on Google users.)
CNET got a “no comment” from the NSA in response to our request for more information.
As TechDirt suggests, an MITM attack on the part of the NSA or GCHQ would hardly be a complete shock. The New York Times reported last week that the NSA has sidestepped common Net encryption methods in a number of ways, including hacking into the servers of private companies to steal encryption keys, collaborating with tech companies to build in back doors, and covertly introducing weaknesses into encryption standards.
It wouldn’t be much of a stretch to obtain a fake security certificate to foil the Secure Sockets Layer (SSL) cryptographic protocol that’s designed to verify the authenticity of Web sites and ensure secure Net communications.
Indeed, such attacks have been aimed at Google before, including in 2011, when a hacker broke into the systems of DigiNotar — a Dutch company that issued Web security certificates — and created more than 500 SSL certificates used to authenticate Web sites.
In any case, the purported NSA/GCHG impersonation of Google inspired a rather clever graphic by Mother Jones, one that might even impress the rather clever Doodlers at Google:
Url to article: http://news.cnet.com/8301-13578_3-57602701-38/nsa-disguised-itself-as-google-to-spy-say-reports/
No talk of changing NSA spy tactics at meeting of new surveillance review panel – report
Published time: September 12, 2013 23:24

View of the National Security Agency (NSA) in the Washington suburb of Fort Meade, Maryland.(AFP Photo / Paul J. Richards)
A new review panel created by President Barack Obama to analyze possible reforms for US government surveillance spoke mainly of tech companies concerns, not National Security Agency spying overreach, during its first meeting.
Attendees of the meeting early this week told the Guardian newspaper discussions were mostly based around the apprehensions and interests of major technology firms. Little about public privacy or real changes to the mass global phone and internet data collection programs was involved.
During the meeting, outside attendees were divided into rights organizations, like the American Civil Liberties Union and the Electronic Privacy Information Center, and the tech companies, including Facebook, Google, Microsoft, Apple and Yahoo. The two groups met in separate locations. Two panelists, Michael Morrell and Richard Clarke, with intelligence backgrounds did not attend the civil liberties meeting. All five panelists attended the tech company session.
Robert Atkinson, the president of the Information Technology and Innovation Foundation attended the meeting and told the Guardian he “did not hear much discussion” of transforming how the NSA collects data from around the world, including America.
“I didn’t find anyone saying the bulk surveillance is horrendous and bad for our democracy,” said Sascha Meinrath, a vice president of the New America Foundation and the director of the Open Technology Institute, who also attended. “The companies are concerned that it impacts their bottom line. My concern is they’re looking to preserve the function of the NSA.”
When asked if that was the perspective of the government or the companies, he responded, “I’m not sure you can separate the two.”
URL to article: http://rt.com/usa/surveillance-review-panel-spying-794/
NSA ‘routinely’ shares Americans’ data with Israel – Snowden leak
Published time: September 11, 2013 15:13
Edited time: September 13, 2013 12:41
The NSA regularly shares raw US intelligence data with Israel without even removing information about American citizens, according to the latest revelation published by the Guardian. The report is based on a document leaked by Edward Snowden.
On Tuesday, September 11, the Guardian published a previously undisclosed document which revealed top-secret policies in place since 2009 that are used to share personal phone and Internet data pertaining to United States citizens with American ally Israel.
The document, a five-page memorandum authorized by the National Security Agency near the beginning of US President Barack Obama’s first administration, outlines a deal between the NSA and Israel’s SIGINT National Unit, or ISNU.
“This agreement,” the memo begins, “prescribes procedures and responsibilities for ensuring” privacy safeguards are implemented to protect the Fourth Amendment rights of US citizens with regards to the direct sharing of raw intelligence collected by the NSA with its Israeli counterpart.
URL to article: http://rt.com/news/nsa-shares-data-israel-723/
NSA spying ‘weakens US security’
Published time: September 12, 2013 14:36
The NSA was no good at decrypting online communications, so they used their authority to spoil encryption technologies to get easy access to communications by people they wanted to spy on, including US citizens, Professor Mathew Green told RT.
A cryptographer at Johns Hopkins University, Professor Mathew Green, had his blog about NSA spying techniques taken down by the university a short while ago.
RT: Professor, before we talk about what happened to your blog, your brief reaction to this revelation of data-sharing with Israel. What do you think Americans will make of the fact that information about them is going to Israel?
Mathew Green: I think what we’re learning is that no matter what we think about the story, we cannot get a fix on it, and the story keeps changing. This is probably the most upsetting part: we don’t know who our data is being shared, and who is spying on whom at this point.
URL to article: http://rt.com/op-edge/nsa-spying-weakens-us-security-768/
NSA can tap into BlackBerry, iOS, and Android systems – report
Published time: September 08, 2013 00:19
Edited time: September 09, 2013 09:04
The US National Security Agency (NSA) can access data on smart phones using the world’s most popular systems including iOs, Android, and even BlackBerry – which markets itself to be highly secure, according to a new report.
The NSA has tapped into all the leading mobile operating systems to gain access to contact lists, SMS traffic, notes, and users’ current and past locations, Der Spiegel reported, citing internal NSA documents.
The leaked information also revealed that the NSA has organized a working group for each operating system. The groups are responsible for clandestine operations to gather data saved on the phones.
URL to article: http://rt.com/news/nsa-smart-phones-spying-563/
Rubio’s okay with NSA spying – Snowden leak is “dangerous”…
Submitted by JO4RP on Fri, 09/13/2013 – 14:30
in
Current Events
Florida
Rubio’s response regarding NSA spying – not what I’d hoped for.
Thank you for taking the time to contact me regarding leaked reports concerning the National Security Agency’s collection programs to safeguard our nation. This is an important issue and I am grateful for your thoughts as well as the opportunity to respond.
As you know, it was recently leaked to the media that the National Security Agency has collected phone record metadata as a tool used to track terrorists. This dangerous national security leak allegedly came from Edward Snowden, a contractor working for the NSA with a top secret security clearance. As we continue to learn about the information that Snowden had access to, it is important to consider both the national security perspective and the protection of individual privacy granted to U.S. citizens through the Constitution. As a member of the Select Committee on Intelligence, I have been briefed on these programs and know that they are valuable tools used by our government to protect the U.S homeland. Please know that I will continue to follow this situation closely and ensure that any privacy concern is heard and addressed appropriately.
It is an honor and a privilege to serve as your United States Senator. I appreciate you offering your opinion on this important issue. If I can ever be of assistance to you, please do not hesitate to contact me.
Sincerely,
Marco Rubio
NSA Follow the Money branch spied on VISA customers, SWIFT transactions report
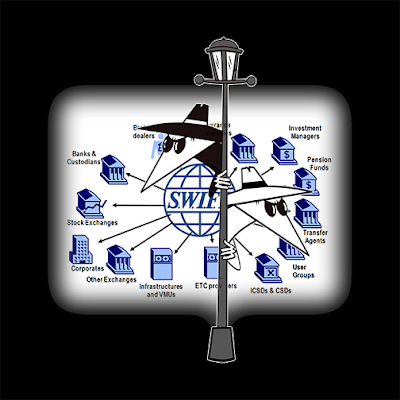
I have one big question to ask… if they had all this inside data what did they do with it? Speculate in the markets? They sure didn’t arrest many bankers! 16 Trillion from the FED and nobody went to jail? When I worked on the VISA transaction system in Foster City, it was well known there were certain VIP cards that were always automatically cleared….
BTW: Bloomberg data shows HSBC owns SWIFT lock-stock-and-barrel… and the vertical integrated market of add-on SWIFT services! -Bill

A Unmanned Aerial Systems is seen during the Defence Security Equipment International (DSEI) arms fair at ExCel in London September 10, 2013.(Reuters / Stefan Wermuth)
Reconnaissance gadgets and robotic warfare devices are getting smaller by the year, with James Bond like technology being offered to a wide range of buyers, from police forces to special military units.
The market place for such technology has become Defence Security and Equipment International (DSEi) exhibition held at ExCel London.
The international exhibition has established itself as the leading platform to view and purchase state of the art equipment from the world’s defense and security industry. Held from September 10-13, it showcased 1,391 exhibitors to almost 30,000 visitors from 121 countries.
This year, the Unmanned Aerial Systems (UAS) conference was also held as part of the DSEi and has focused on future capabilities, including civilian applications of drones as well as technological innovations. The UAS 2,000 m2 event became a one-stop store for anyone seeking to work with the Remotely Piloted Air Systems industry. The Unmanned Systems Showcase held number demonstrations of Unmanned Aerial Vehicles (UAVs) and Unmanned Ground Vehicles, as well as other gadgets that are to be deployed in various security environment and scenarios.
“Technological advances, operational imperatives and budgetary constraints are driving ever greater reliance on UAVs in military operations. UAVs are increasingly being depended upon to deliver capabilities that formerly relied on manned platforms. As their strategic importance increases, the UAS industry must respond to deliver systems that are ever more cost effective, dependable and survivable,”one of the sponsors of the event, Cranfield University, said at the conference.
As unmanned drones continue to make headlines on the battlefield in the US-led war on terror over the skies of Afghanistan, Yemen and Pakistan, the industry’s main goal is to expand the market share of robots to law enforcement and other security industries.

AFP Photo / Jack Guez
American companies such as Lockheed Martin, Northrop Grumman and General Atomics continue to dominate the military market, while other defense firms such as BAE Systems are in pursuit to develop the next-generation drones with stealth capabilities.
But it is the smaller players on the market that are expending the robotic frontiers with their drive to perfect underwater robots that can that can be used on the seabed to clear mines or gather reconnaissance. The inventions are getting so tiny that a newly exhibited “quadrocopter” with four or more rotors can be activated from backpacks via remote control.
One of the aim of the technological innovations is to make warfare more secure and safe.
For instance, the ReconRobotics firm says their latest product, the ThrowbotXT is designed to detect an explosive or hostiles in a building before soldiers or police are sent in to secure the premises. The company has sold more than 4,000 of these devises, mostly to the US military in Afghanistan.
The personal sensor system for tactical operators is “pound-for-pound, the most versatile, robust, stealthy and easy-to-deploy tactical robot system in the world,” the company says.
Once deployed, the micro-robot transmits video and audio to the controller allowing the analyst to “spot armed subjects, confirm the presence of hostages or innocent civilians, listen in on conversations, and reveal the layout of rooms”
“It gives you eyes inside a room before you go there,” Ernest Langdon director of US and international military programs for the company told Reuters. “Maybe that means you see there are children in a room so you don’t throw a grenade. Maybe it means you find an IED (improvised explosive device).”

A man looks at a Shepherd-MIL Unmanned Aerial Vehicle (UAV) during the Defence Security Equipment International (DSEI) arms fair at ExCel in London September 10, 2013.(Reuters / Stefan Wermuth)
ReconRobotics’ is in the process of developing a flying quadrocopter tiny enough to fit in a backpack but capable of providing surveillance inside a structure. Similar designs were also showcased by Estonia’s Eli Airborne Solutions used by the country’s border guard and aimed for exports to Latin America countries.
Other companies such as the British Colena, are trying to break into a non-military market and are targeting show business. Their five-rotored radio-controlled copter is designed to for the use of film production studios by offering views over battlefields and facial recognition software to scan crowds at public events.
“You see it at the end where you have small robots to be thrown through a window and you see it at the higher end where you have large, expensive drones with artificial intelligence designed to operate for hours or even days at a time,” Douglas Barrie, air power analyst at London’s International Institute for Strategic Studies told Reuters
“This UK MOD initiative aims to facilitate pragmatic and expedient test and evaluation solutions to a wide range of emerging issues ranging from operational capability problems through to studies pertaining to future UAS test and evaluation,” Defence Unmanned Air Systems Capability Development Centre said about the exhibition.

A protester carries a poster during a demonstration against the Defence and Security Equipment International (DSEI) arms fair at the ExCeL centre in east London, on September 10, 2013.(AFP Photo / Ben Stansall)
This year’s event has been highly politicized as major powers lock horns over the US’s attempt to strike Syria over the alleged use of chemical weapons. But it was not the US, responsible for massive collateral damage from the drone warfare that was under pressure. Instead, it was Russia, which the organizers thought should have a limited space for presentation at the event, due to its military contracts with the Syrian government.
“We can confirm categorically that Rosonboronexport is not exhibiting at DSEI 2013,” organizers said in a statement. As a result, only five Russian companies were registered to exhibit that are classified as humanitarian and rescue organizations. They include EMERCOM – an Russian organisation engaged in humanitarian and rescue activity around the world; Concern SYSTEMPROM – manufacturers of communication and control systems; Kovrov Electronmechanical Plant – manufacturers of bomb disposal robots, electrohydraulic systems for stabilisation, and GPS systems; MDB COMPAS – manufacturers of navigation equipment for aircraft; and RPC ISTOK – manufacturers of microwave communications components.
Because many of the exhibitors were from the arms industry, the event attracted a throng of anti-war and anti-drone protesters. Arguing that robotic warfare eliminates ethical factor in combat by making it too easy to kill innocent people, hundreds protested next to Excel centre for the duration of the conference.
The rally, titled “Say No to the Games of Drones”, was organized by War on Want, Campaign Against Arms Trade, Drone Wars UK, Stop the War Coalition and Campaign for Nuclear Disarmament.
“Drones are indiscriminate weapons of war that have been responsible for thousands of civilian deaths. Drones should be banned, just as landmines and cluster munitions were banned. Now is the time to stop the rise of drone warfare – before it is too late,” War on Want said in a statement.
Armed drones were first used in late 2001 by Washington inside Afghanistan. Since then, drones have been deployed by the US and its allies in Pakistan, Yemen, and Somalia. It is estimated that the United States has killed around 4,700 people in drone strikes.
URL to article: http://rt.com/news/drone-exhibition-uk-protest-840/
Ten Things We’ve Learned About The NSA From A Summer Of Snowden Leaks
Andy Greenberg, Forbes – 9/9/2013
“The truth is coming, and it cannot be stopped,” Edward Snowden told readers of the Guardian in June. At the time, just a few weeks into the publication of documents that the 30-year-old former National Security Agency contractor had siphoned from his workstation in Hawaii, that prophetic statement might have seemed like grandstanding. But close to three months later, the collection of Snowden’s revelations has grown to the megaleak proportions of WikiLeaks’ Cablegate or Daniel Ellsberg’s Pentagon Papers,with no end in sight. For those who watch the watchers, Snowden may well have become the most important leaker of the 21st century.
Snowden himself has managed to take refuge in Russia and disappear from the headlines, putting the full spotlight back onto his bombshell documents. But as with all megaleaks, the sheer number of scoops he’s enabled threatens to overwhelm anyone tracking the NSA’s still-growing scandal. Here are a few highlights from what we’ve learned so far in the Summer of Snowden.
- For more than a decade, the NSA has been working to systematically influence encryption standards or insert backdoors in the code of commercial encryption software to enable it to access Internet users’ communications, according to documents Snowden leaked to the Guardian, which were shared with the New York Times and Pro Publica. Though the published documents lack many details, the protocols the agency may have the ability to break or circumvent include Web encryption such as Secure Sockets Layer and Transport Security Layer, the Internet protocol encryption and authentication technology IPsec, common virtual private network systems used for anonymity and secure remote access, and Voice-Over-Internet-Protocol. (VoIP) The backdoor-planting projects, known as “Bullrun” in the United States and “Edgehill” within the NSA’s British equivalent the GCHQ, have made “vast amounts of encrypted Internet data…exploitable,” according to one leaked document.
- The German newsweekly Der Spiegel wrote over the weekend that it had obtained NSA documents revealing that the agency has the ability to access a wide range of information stored on smartphones including iPhones, Blackberrys, and those running Google’s Android operating system. That information includes contacts, text message traffic, and location data–the paper alludes to the NSA’s compromise of “38 iPhone features.” Despite losing access to Blackberry’s messaging systems in 2009 after a change in how the company compressed data, the agency noted in a document that a breakthrough allowed it to regain access in 2010.
- Snowden-leaked documents obtained and partially published by theWashington Post revealed the makeup of the so-called Black Budget, the $52.6 billion of government funding spent on classified programs. The budget showed that the NSA received $10.8 billion for the year 2013, second only to the CIA’s $14.7 billion. The budget confirmed that the NSA employs an elite hacking team it calls Tailored Access Operations, revealed the agency’s focus on hacking network routers and switches rather than servers and PCs, and exposed a program to combat “insider threats” by investigating 4,000 employees, which was (ironically) shelved to focus on reacting to WikiLeaks’ disclosures in 2010. The budget also outlined how much telecom firms are paid for their cooperation with the NSA’s surveillance.
- Newly-revealed surveillance targets for the NSA, according to various Snowden leaks, include the presidents of U.S.-friendly countries such as Brazil and Mexico, international organizations like the U.N. and E.U.–going so far as to bug embassies and hack the U.N.’s video conferencing systems–and Al Jazeera, the first revelation that the NSA has surveilled journalists. Earlier leaks, published by the Guardian, included a program that mapped out the frequency of NSA’s surveillance by country, showing a focus on the Middle East but also including American targets. Another document confirmed that President Obama has asked the NSA to draw up a list of potential cyberattack targets, including ones that could potentially disable enemy infrastructure.
- Internal audit documents from the NSA, obtained by the Washington Post, show that the agency found 2,776 incidents in which its staff had broken its own rules governing surveillance in the year leading up to May 2012. In one case, a surveillance operation continued for three months before the Foreign Intelligence Surveillance Court, which is designed to oversee the agency, first heard about it and ruled it unconstitutional. In another comic example, analysts collected phone calls from the Washington area because its “202″ area code was confused with Egypt’s country code, “20.”
- Even when the NSA follows its internal rules, it’s offered a surprising number of regulatory loopholes. A document published by the Guardian showed that the NSA makes broad exceptions to its mission of only spying on foreign targets. That includes collecting and storing information on Americans when it’s judged to contain “significant foreign intelligence” information, information about a crime that has been or may be about to be committed, is related to “the unauthorized disclosure of national security information,” or is involved in assessing “a communications security vulnerability.” In another exception, any encrypted data can also be held long enough to crack it.
- Documents given to the Guardian revealed that the NSA helps to fund the spying operations of Britain’s GCHQ, in part to take advantage of the U.K.’s more relaxed regulations of its intelligence sector. Over three years, the NSA gave more than $150 million to British intelligence services, and 60% of GCHQ’s “refined intelligence” also reportedly came from the NSA’s analysis.
- Other documents focusing on GCHQ and published by the Guardian showed that the British intelligence service has the ability to tap transatlantic fiberoptic cables for raw Internet data, much of which is shared with the NSA.
- In a slideshow first published in part by the Washington Post, a program known as PRISM reportedly allowed direct access to the servers of companies including Google, Apple, Facebook, Microsoft, and others. Most of the companies implicated in PRISM denied any such access, but several, including Apple and Facebook, responded by offering details for the first time about how often they cooperate with surveillance requests from the NSA and from law enforcement.
- The Guardian kicked off the Snowden saga in June with an order sent to Verizon on behalf of the NSA demanding the cell phone records of all of Verizon Business Network Services’ American customers for a three month period. The order, which dealt with only those users’ metadata,specifically requested Americans’ records. In the following days, Senators Saxby Chambliss and Diane Feinstein publicly stated that similar orders have been issued to telecoms for the last seven years.
URL to article: http://www.forbes.com/sites/andygreenberg/2013/09/09/ten-things-weve-learned-about-the-nsa-from-a-summer-of-snowden-leaks/
Argentina, Brazil agree on cyber-defense alliance against US espionage
Published time: September 15, 2013 03:30
Defense ministers of Brazil and Argentina have pledged to cooperate closely to improve cyber defense capabilities following revelations of the scale of US spying on Latin American countries.
“We need to reflect on how we cooperate to face these new forms of attack,” Brazil’s defense minister, Celso Amorim, said at a conference in Buenos Aires.
“We have established that we will hold a meeting in Brasilia before the end of the year to intensify our complementarity in the matter of cyber defense,” Argentine defense minister Agustin Rossi said after talks with his Brazilian counterpart.
The ministers signed a broader military cooperation agreement on Friday.
URL to article: http://rt.com/news/brazil-argentina-cyber-defense-879/
Related
Zuckerberg Admits Gov “Blew It” When Snowden Revealed PRISM
Facebook reportedly considering adding 1+ billion members’ photos to facial recognition database
DISCLOSURE: DEA using ‘terrorism’ surveillance to entrap Americans
DISCLOSURE: NSA now admits spying on 75% of U.S. Internet traffic: Emails, texts, voice calls
SITS: Before its News: NSA Charging You to Spy on You
SITS: WIRED.COM: Internet Giants Got Millions From Taxpayers to …
SITS: Info Wars: Obama’s Response To NSA Was To Appease The …
SITS: More Unwarranted Spying on the World – House rejects bid to …







Leave a Reply